Analyze page
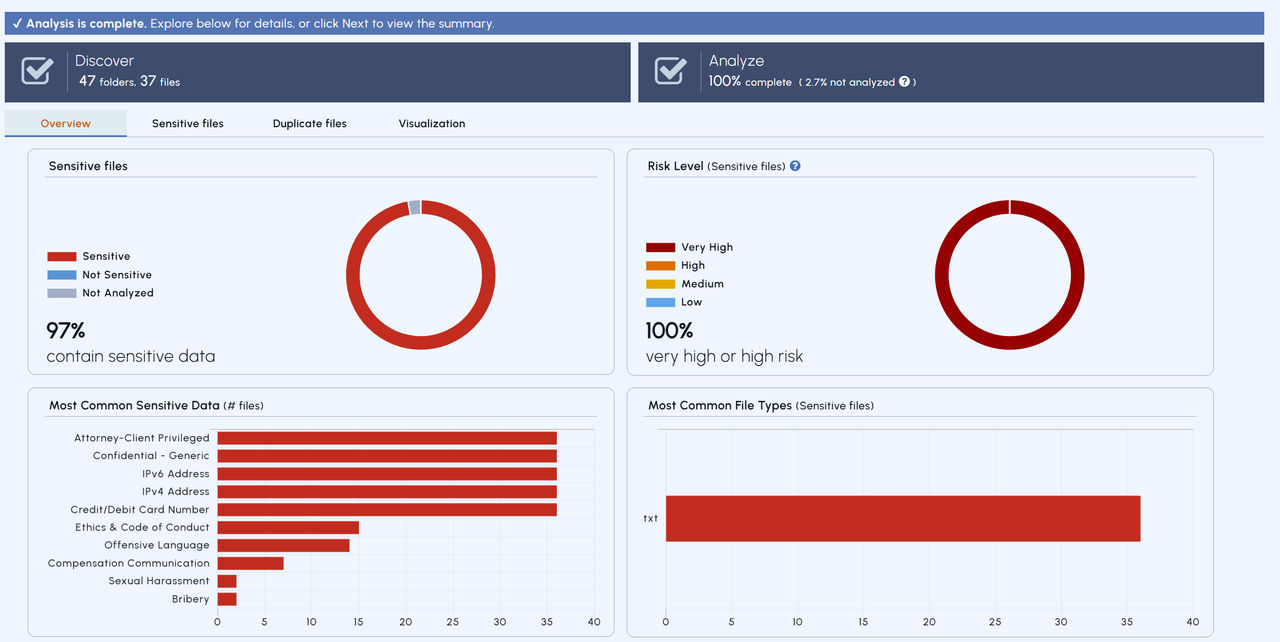
The Analyze page provides information on potentially sensitive files through different tabs as shown in following table:
| Tab | Details for analyzed sensitive files |
|---|---|
| Overview | - A donut chart that shows sensitive and non-sensitive files |
| - A donut chart that shows the risk level associated with all sensitive files, excluding 'No Risk' files, based on their risk level. | |
| - A bar chart that shows the most common file extensions within sensitive files | |
| - A bar chart that shows the top 10 patterns or policy conditions based on hits for sensitive files | |
| - A bar chart that shows the last modified date for sensitive files | |
| - A bar chart that shows the file sizes for analyzed sensitive files | |
| - A bar chart that shows sentiment score buckets on X-axis and number of files in each bucket on Y-axis | |
| Sensitive Files | List of sensitive files with their individual risk levels and risk scores |
| Duplicate Files | List of duplicate files with their individual risk levels and risk scores |
| Visualization | Word cloud of all entities, patterns, and policy conditions based on number of hits, along with People and locations. |
| Sentiment Score ** | List of files with their sentiment scores |
| ** Sentiment Score tab is visible only if Analyze sentiment checkbox is selected for a particular analysis. |
The following image shows the details displayed in the Overview tab of the Analyze page:
 |
|---|
Following image shows the details displayed on the Summary page:
 |
|---|
You can download the CSV without including match details. To include match details, check the box and click Download CSV.
 |
|---|
After downloading the CSV, check the download status from your browser and open the file. If you have not included match details, the CSV column headers will appear as shown in the following image:
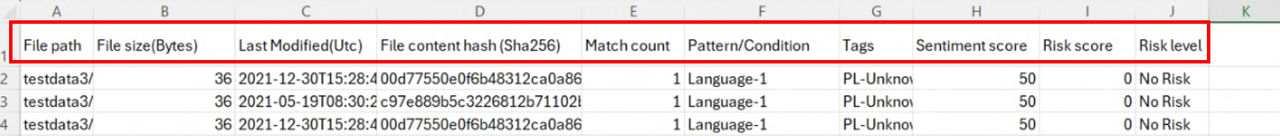 |
|---|
If you have included match details, the CSV column headers will appear as shown in the following image:
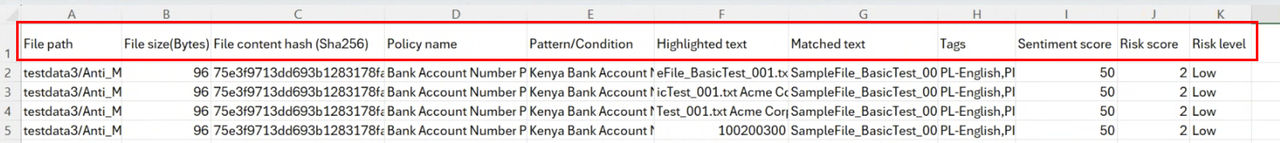 |
|---|
The Summary page provides the analysis summary of potentially sensitive files. It also provides options to download reports for Compliance Analysis in CSV format.
Related information